n Introduction to Groups
A group can be defined as a collection of accounts that are grouped together so that Administrators can assign permissions and rights to the group as a single entity. This removes the need for an Administrator to individually assign permissions and rights to each account. Therefore, while a user account is associated with an individual, or one entity; a group account or a group, is created to simplify the administration of multiple user accounts (users). When you grant permissions to a group, all accounts that are part of that particular group are granted the permissions. Permissions actually controls which actions users can perform on a network resource. Rights on the other hand relate to system tasks.Windows Server 2003 provides user accounts and group accounts (of which users can be a member). User accounts are designed for individuals. Group accounts are designed to make the administration of multiple users easier.
The following entities can be added to groups:
- User accounts
- Computer accounts
- Contacts
- Other group's members
- Other groups
- Assign permissions to groups to access shared resources. Each group member would be able to access the shared resources.
- Assign rights to groups so that they can perform certain system tasks such as backing up or restoring files.
- Groups are also used to distribute bulk e-mail to its members.
Group Types
You can create two types of groups in Active Directory. Each group type is used for a different purpose. Security groups are the group type which is created for security purposes, while distribution groups is the group type created for purposes other than security purposes. Security groups are typically created for assigning permissions, while distribution groups are usually created for distributing bulk e-mail to users. As you can see, the main difference between the two groups is the manner in which each group type is used. Active
- Security groups: A security group is a collection of users who have the same permissions to resources, and the same rights to perform certain system tasks. These are the groups to which you assign permissions so that its members can access resources. Security groups therefore remove the need for an Administrator to individually assign permissions to users. Users that need to perform certain tasks can be grouped in a security group, and then assigned the necessary permissions to perform these tasks. Each user that is a member of the group would have the same permissions. In addition to this, any e-mail sent to a security group is received by each member of that particular group. When a security group is first created, it receives a SID. It is this SID that enables permissions to be assigned to security groups – the SID can be included in the DACL of a resource. An access token is created when a user logs on to the system. The access token contains the SID of the user, and the SID of those groups to which the user is a member of. This access token is referenced when the user attempts to access a resource – the access token is compared with the DACL of the resource to determine which permissions the user should receive for the resource.
- Distribution groups: Distribution groups are created to share information with a group of users through e-mail messages. Thus, a distribution group is not created for security purposes. A distribution does not obtain a SID when it is created. Distribution groups enable the same messag to be simultaneously sent to its group members – messages do not need to be individually sent to each user. Applications such as Microsoft Exchange that work with Active Directory can use distribution groups to send bulk e-mail to groups of users.
Group Scopes
The different group scopes make it possible for groups to be used differently to assign permissions for accessing resources. The scope of a group defines the place in the network where the group will be used or is valid. This is the degree to which the group will be able to reach across a
In Active Directory, there are three different group scopes.
- Global groups: Global groups are containers for user accounts and computers accounts in the domain, and are used to assign permissions to objects that reside in any domain in a tree or forest. You can include a global group in the access control list (ACL) of objects in any domain in the tree/forest. A global group can however only have members from the domain in which it is created. What this means is that a global group cannot include user accounts, computer accounts, and global groups from other domains.
The domain functional level set for the domain determines which members can be included in the global group.
- Windows 2000 Mixed: Only user accounts and computer accounts from the domain in which the group was created, can be added as group members.
- Windows 2000 Native / Windows Server 2003: User accounts, computer accounts, and other global groups from the domain in which the group was created, can be added as group members
- Windows 2000 Mixed: Only user accounts and computer accounts from the domain in which the group was created, can be added as group members.
- Domain Local groups: Domain local groups can have user accounts, computer accounts, global groups, and universal groups from any domain as group members. However, you can only use domain local groups for assigning permissions to local resources, or to resources that reside in the domain in which the domain local group was created. This means that you can only include domain local groups in the ACL of objects that are located in the local domain.
The domain functional level set for the domain determines which members can be included in the domain local group.
- Windows 2000 Mixed: User accounts, computer accounts, and global groups from any domain can be added as group members.
- Windows 2000 Native / Windows Server 2003: User accounts, computer accounts, global groups, and universal groups from any domain can be added as group members. You can also add other domain local groups from the same domain as group members.
- Windows 2000 Mixed: User accounts, computer accounts, and global groups from any domain can be added as group members.
- Universal groups: Universal groups can have user accounts, computer accounts, global groups, and other universal groups, from any domain in the tree or forest as members. This basically means that you can add members from any domain in the forest to a universal group. You can use universal groups to assign permissions to access resources that are located in any domain in the forest. Universal groups are only available when the domain functional level for the domain is Windows 2000 Native or Windows Server 2003. Universal groups are not available when domains are functioning in the Windows 2000 Mixed domain functional level. You can convert a universal group to a global group or to a domain local group if the particular universal group has no other universal group as a group member. When adding members to universal groups, it is recommended to add global groups as members and not individual users.
- Windows 2000 Mixe:
- Global groups: User accounts and computers accounts in the same domain.
- Domain local groups: User accounts, computers accounts, and global groups from any domain.
- Global groups: User accounts and computers accounts in the same domain.
- Windows 2000 native or Windows Server 2003:
- Global groups: User accounts, computer accounts, and other global groups in the same domain.
- Domain local groups: User accounts, computers accounts, global groups and universal groups from any domain; and other domain local groups in the same domain.
- Universal groups: User accounts, computers accounts, global groups, and universal groups from any domain.
- Global groups: User accounts, computer accounts, and other global groups in the same domain.
- You can convert domain local groups and global groups to universal groups
- You can convert universal groups to domain local groups or to global groups.
- You cannot convert domain local groups to global groups.
- You cannot convert global groups to domain local groups.
- The default domain local groups that are created are listed below:
- Cert Publishers: Members of this group are able to publish certificates to Active Directory
- DnsAdmins: Group members have administrative access to the DNS server service.
- HelpServicesGroup: Group members are able to assign rights to support applications.
- RAS and IAS Servers: Servers assigned to this default group can access a user's remote access properties.
- TelnetClients: Group members have administrative access to Telnet Server.
- Cert Publishers: Members of this group are able to publish certificates to Active Directory
- The default global groups that are created are listed below:
- Domain Admins: Members of the Domain Admins group have permissions to perform administrative functions on computers in the domain.
- Domain Users: Group members are user accounts that are created in the domain.
- Domain Computers: Group members are computer accounts that are created in the domain. This includes all workstations and servers that are part of the domain.
- Domain Controllers: Group members are domain controllers of the domain.
- Domain Guests: Group members are guest accounts in the domain.
- Group Policy Creator: Group members are able to change the domain's group policy.
- DnsUpdateProxy: Group members are DNS clients. Members are able to perform dynamic updates for clients such as DHCP servers.
- Domain Admins: Members of the Domain Admins group have permissions to perform administrative functions on computers in the domain.
- The default universal groups that are created are listed below:
- Enterprise Admins: Members of this group are able to perform administrative functions for the whole network.
- Schema Admins: Members of this group can perform administrative tasks on the schema.
- Enterprise Admins: Members of this group are able to perform administrative functions for the whole network.
- You should add users that perform the same function in the organization to a global group.
- Domain local groups should be created for a resource(s) that needs to be shared by multiple users.
- You should then add any global groups that have to access a resource(s) to the appropriate domain local group.
- The domain local group should be assigned with the proper permissions to the resource.
How to create a group
You can use the Active Directory Users And Computers console to create a new group. After the group is created, you can set additional properties for the group, and add members to the group.To create a new group,
- Click Start, Administrative Tools, and then Active Directory Users And Computers.
- Right-click the particular domain, organizational unit, or container in which you want to place the new group, and select New, and then Group from the shortcut menu.
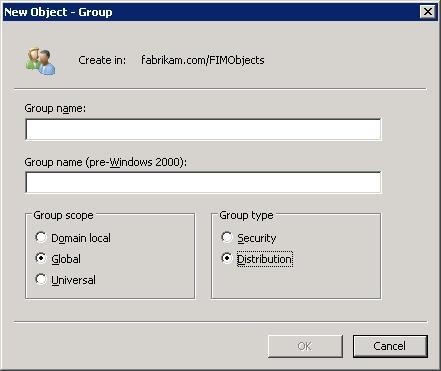
- The New Object-Group dialog box opens next.
- In the Group Name box, enter a name for the new group. You can specify a name as long as 64 characters.
- The Group Name (Pre-Windows 2000) box is automatically populated with the first 20 characters of the group name that you specified.
- In the Group Scope box, select one of the following options as the group scope: Domain Local, Global, or Universal.
- In the Group Type box, select one of the following options as the group type: Security or Distribution.
- Click OK.
How to add multiple members to a group
- Click Start, Administrative Tools, and then Active Directory Users And Computers.
- Expand the particular domain, organizational unit, or container that contains the group that you want to add members to.
- Locate and right-click the group, and then select Properties from the shortcut menu.
- When the Properties dialog box opens, click on the Members tab.
- Click Add.
- When the Select Users, Contacts, Computers, Or Groups dialog box opens, click the Advanced button.
- Click the Find Now button and select the user accounts, group accounts, or computer accounts that should be added to the particular group. If you want to select multiple users, groups, or computers, simply hold down the Shift or Ctrl key.
- Click OK.
- Each account that you have selected now appears in the Enter The Object Names To Select box.
- Click OK to add the members to the group.
- Click OK in the Properties dialog box for the group.
How to manage group membership individually
- Click Start, Administrative Tools, and then Active Directory Users And Computers.
- Double-click the user, group, or computer account that you want to work with.
- When the Properties dialog box opens, click the Members Of tab.
- If you want to add this particular account as a member of a group, click Add.
- When the Select Groups dialog box opens, select the groups that this account should be member of.
- If you want to remove the account from a group, simply click Remove
- Click OK.
How to delete a group
When it comes to deleting a group, you should remember the following points:- When a security group is created, it receives a unique SID. When you delete a group, the SID of that particular group is never used again, even if you create a group with the same name at a later stage.
- When a group is deleted, the following are deleted:
- The actual group being deleted
- All permissions/rights associated with the particular group being deleted
- The actual group being deleted
- When a group is deleted, the following are not deleted:
- Any user accounts and computer accounts that are members of the particular group.
- Any user accounts and computer accounts that are members of the particular group.
- Click Start, Administrative Tools, and then Active Directory Users And Computers.
- Expand the particular domain, organizational unit, or container that contains the group that you want to delete.
- Locate and right-click the group, and then select Delete from the shortcut menu.
- Click Ys to verify that you want to delete the particular group.
How to change the group scope of an existing group
You can change the group scope of existing groups when the domain functional level is set to Windows 2000 native or Windows Server 2003.- Click Start, Administrative Tools, and then Active Directory Users And Computers.
- Expand the particular domain, organizational unit, or container that contains the group that you want to change the group scope for.
- Locate and right-click the group, and then select Properties from the shortcut menu.
- When the Properties dialog box opens, on the General tab, change the group scope in the Group Scope box to either Domain Local, Global, or Universal.
- Click OK.
How to change the group type of an existing group
You can convert a group's type from being a security group to a distribution group, or from being a distribution group to a security group- Click Start, Administrative Tools, and then Active Directory Users And Computers.
- Expand the particular domain, organizational unit, or container that contains the group that you want to change the group type for.
- Locate and right-click the group, and then select Properties from the shortcut menu.
- When the Properties dialog box opens, on the General tab, change the group type in Group Type box to either Security or Distribution.
- Click OK
How to manage group scope, group type, and group membership using the command-line
You can use dsget group to determine and view the properties of groups in Active Directory.- To determine the scope of a group, use the syntax listed below:
- dsget group -scope
- dsget group -scope
- To determine the group type of a group, use the syntax listed below:
- dsget group -secgrp
- dsget group -secgrp
- To determine the members of a particular group, use the syntax listed below:
- dsget group -members
- dsget group -members
- To determine a group's membership, use the syntax listed below:
- dsget group -memberof
- dsget group -memberof
- To change a group's type, use the syntax listed below:
- dsmod group GroupDN [-secgrp {yes | no}]
- dsmod group GroupDN [-secgrp {yes | no}]
- To change a add new members to a group, use the syntax listed below:
- dsmod group GroupDN -addmbr UserDN
- dsmod group GroupDN -addmbr UserDN
- To remove existing members from a group, use the syntax listed below:
- dsmod group GroupDN -rmmbr UserDN
- dsmod group GroupDN -rmmbr UserDN
Không có nhận xét nào:
Đăng nhận xét